All articles containing the tag [
Waf
]-
Security Protection Practice: A Collection Of Methods To Effectively Defend Against Common Network Attacks On Us Www Servers
this article systematically introduces a collection of methods to effectively defend against common network attacks on us www servers, including practical suggestions such as server hardening, network boundary protection, application layer waf, authentication and access control, log monitoring and emergency recovery.
us www server security protection network attack defense ddos protection waf ssh hardening log monitoring backup and recovery -
Enterprise-level Procurement Reference Japanese Server Network Type Security And Redundancy Solutions
reference for japanese server network types, network security and redundancy solutions for enterprise-level procurement. covers bandwidth and line redundancy, ddos protection, multi-machine rooms and bgp, multi-layer authentication, backup and compliance points to help it decision-makers formulate robust solutions.
japanese servers enterprise-level procurement network types redundancy solutions security design ddos protection multi-machine rooms bgp multi-line backup and disaster recovery -
Comparative Analysis Report On The Anti-attack Capabilities Of Bgp High-defense Us Servers And Ordinary Hosts
professionally compares the anti-attack capabilities of bgp high-defense us servers and ordinary hosts, and provides analysis and suggestions from the aspects of bgp principles, traffic cleaning, network layer and application layer protection, scalability, geo factors and operation and maintenance complexity.
bgp high defense us server anti-attack capability ordinary host ddos protection network security geo optimization high defense comparison -
From The Perspective Of Technical Implementation, Network Architecture Suggestions For Hong Kong Site Group Multi-ip Servers To Be Exempted From Registration
discuss the network architecture recommendations for hong kong site clusters and multi-ip servers from the perspective of technical implementation, focusing on compliance, performance and security. it does not provide specific methods to avoid filing, and it is recommended to deploy within the legal framework.
hong kong site group multi-ip server network architecture filing compliance cdn dns operation and maintenance -
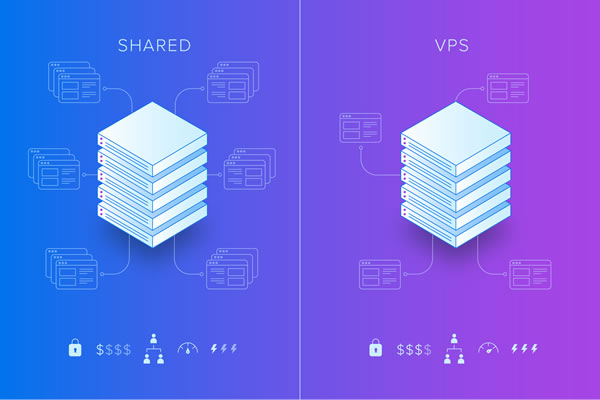
Detailed Explanation Of Malaysia Server Settings And Firewall Strategies In Vps Environment From Scratch
detailed explanation of malaysian server settings and firewall strategies in vps environment from scratch, including node selection, system configuration, network and storage optimization, ssh and protection, iptables/nftables practice, application layer protection and monitoring suggestions to help improve availability and security.
malaysia vps vps settings malaysia servers firewall policies ssh security iptables nftables waf network optimization data sovereignty -
Recommended Server Types And Configuration Strategies For Hong Kong Website Clusters For Seo And Marketing
introduces the types and configuration strategies of hong kong site cluster servers for seo and marketing, covering practical suggestions such as independent servers, vps, cloud hosts, cdn and ip geolocation, to help improve the effects of hong kong geo and site clusters.
hong kong station group server hong kong server station group server seo optimization geo optimization marketing server server configuration -
Practical Methods For Network Acceleration And Global Traffic Scheduling Of Amazon Cloud Servers In Singapore
practical methods for amazon cloud server network acceleration and global traffic scheduling for singapore nodes, covering practical suggestions such as acceleration technology selection, scheduling strategy, monitoring and testing, security and compliance.
singapore amazon cloud server network acceleration global traffic scheduling cdn routing optimization performance optimization multi-region deployment -
Security And Backup Solutions For Enterprise-level Websites Using The Us Cn2 Site Group
this article focuses on the security and backup solutions for enterprise-level websites after adopting the us cn2 site cluster, covering network isolation, encryption, backup strategies, disaster recovery drills and compliance audits, and provides executable suggestions for site cluster deployment.
enterprise-level website us cn2 site group security backup disaster recovery rto rpo encryption operation and maintenance monitoring -
Cera, The First Choice For Game Hosting, Analyzes The Us High-defense Server Architecture And Anti-attack Strategies
this article analyzes the architecture and anti-attack strategies of cera, the us high-defense server that is the first choice for game hosting, covering network boundary protection, traffic cleaning, application layer defense, operation and maintenance monitoring and geo optimization suggestions to help developers and operation and maintenance achieve stable and low-latency game hosting services.
cera us high defense server game hosting high defense server architecture ddos protection game server attack resistance geo optimization network security